OpeniPhone
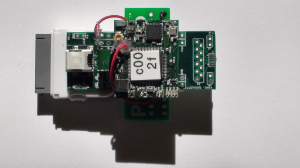
We have been looking for a few months at the best way to add an IEEE802.15.4 interface to a smart phone. This article details the steps to do so on a iPhone. Specifically, we use a GINA mote running the OpenWSN stack; the jailbroken iPhone runs Python script which is is part of OpenWSN.
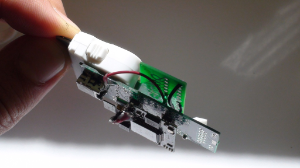
Step 1: building the hardware
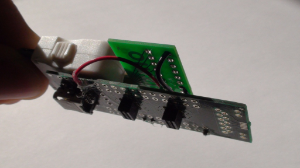
The 30-pin connector on the bottom of the iPhone contains a 3.3V TTL-level UART (2 pins, one Tx, one Rx) as well as a 3.3V and a ground line. The physical interconnection between the iPhone and the GINA mote (or any mote which has a UART link) consists of 4 wires.
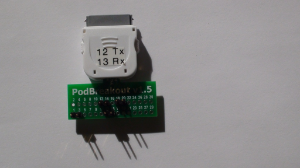
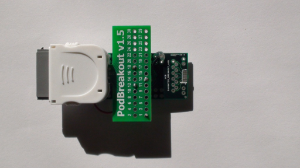
We use a breakout-board for the iPhone connector called PodBreakout1.5, which is sold by Sparkfun. You can find the pinout here.
We solder wires to connect pins 1, 18, 12 and 13 from the PodBreakout1.5 to the +3V, GND, P3.7 and P3.6 pins of the GINA-breakout, respectively. Remember to cross the UART Tx and Rx lines, such that the Tx lines of the PodBreakout1.5 goes into the Rx lines of the GINA-breakout, and vice-versa.
We hot glue GINA-breakout onto the PodBreakout1.5.
The GINA mote fits into the male connector of the GINA-breakout.
Step 2: JailBreaking your iPhone
"JailBreaking" an iPhone modifies its operating system (iOS) and allows it to run applications which have not been previously approved by Apple. It is both reversible and legal in the USA. We require a JailBroken iPhone to be able to interact with the UART link, something which can not be done through iOS. More specifically, iOS does allow you to interact through UART with iPhone accessories, but for those accessories to be recognized by the iPhone, they need to contain an authentication chip provided by Apple. Considering this limited proof-of-concept experiment, we haven't been able to obtain such chips from Apple.
You need your iPhone to run iOS version 4.0.1 or below. To jailbreak it, use your iPhone's browser to navigate to http://jailbreakme.com/, then slide the"slide to jailbreak" slider. The JailBreaking process is completely automated, and takes 5-10 min. Because it involves downloading Linux packages, it's a good idea to have your iPhone connected to a WiFi network when you do this. For more information, read http://jailbreakme.com/faq.html.
When the JailBreaking process is finished, a Cydia icon appears on your springboard. This acts as a Linux packet manager, and is the equivalent of Apple's App Store.
Open Cydia and follows the posts on the welcome screen of how to change your iPhone's password, and how to transfer files to/from the iPhone (we use WinSCP).
Use Cydia to install the following packages:
OpenSSHallows you to connect remotely to your iPhone using PuTTY, a text-based Linux equivalent of Windows' remote desktop application.- Vi IMproved (
vim) is a simple text editor so you can open files while connected to your iPhone through SSH; PyObjCis a package which converts Python code you write into Obective C, the C dialest the iPhone understands;iPhone/Pythonis an example Python program written by saurik from UC Santa Barbara, showcasing the use of PyObjC.
Step 3: programming the iPhone
Download the OpenWSN source code. Using WinSCP, drag-and-drop the OpenWSN.app/ folder into the iPhone's /Applications/ folder. To refresh the springboard and have the Cal logo show (see picture above), log into to your iPhone using PuTTY, switch to user mobile and type uicache.
Step 4: running the application
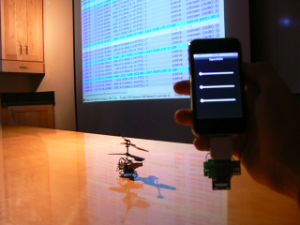
This application allows you to remote-control a helicopter controlled by a GINA mote running the OpenWSN stack. In particular, it sends UDP packets to the application Heli which listens to UDP port 2192.
This application expects 4 bytes of payload:
- the first 2 bytes represent a 16-bit unsigned integer (big-endian) which controls speed of the upper rotor.
- the second 2 bytes control the speed of the lower rotor.
The higher the number, the faster the rotor, with a maximum value of 100. A value 0 stops the rotor.
The graphical interface consists of 3 sliders:
- the top one for the top rotor.
- the lowest for the lower rotor.
- the center slider to control both rotors at the same time.
Once you connect the hardware, moving the position of a slider causes a UDP packet to be sent to the IPv6 address of the helicopter, which sets its rotors accordingly.
In the YouTube video above, the projector screen shows the stream of packets which travel over the air, captured using Wireshark.
Please direct questions to Thomas Watteyne.